We previously showed in detail how to use SSL encryption with the Impala or Hive Editors. Here is now a step by step guide about how to use LDAP authentication instead of no authentication or Kerberos.
Note: this requires Hue 3.7 or CDH5.2
HiveServer2 had SSL enabled so Hive Editor could not connect to HiveServer2. HiveServer2 logs showed SSL errors indicating that it received plaintext (good hint at the cause)
Solved by adding this to the Hue Safety Valve:
(validate was false since their certificates used wildcards and this caused other errors)
Note: If not using SSL, you will hit this bug: HUE-2484
The same Hue behavior occurred after making the change, but now the HiveServer2 log showed authentication failure due to err=49
So, we added the following to the Hue Safety Valve:
[beeswax]
[[ssl]]
\## Path to Certificate Authority certificates.
cacerts=/etc/hue/cacerts.pem
\## Choose whether Hue should validate certificates received from the server.
validate=false
or
[impala]
[[ssl]]
\## SSL communication enabled for this server.
enabled=false
\## Path to Certificate Authority certificates.
cacerts=/etc/hue/cacerts.pem
\## Choose whether Hue should validate certificates received from the server.
validate=false
Hue still showed the same behavior. HiveServer2 logs showed:
is not allowed to impersonate bob
We solved this by adding the following to the HDFS > Service-Wide ->Advanced>Safety Valve for core-site.xml.
hadoop.proxyuser..hosts
*
hadoop.proxyuser..groups
*
After this, the default database was displayed, but we could not do a show tables; or anything else. Beeline had the same behavior.
We did a grant for the group to which the user who was attempting the Hive actions and then that problem went away.
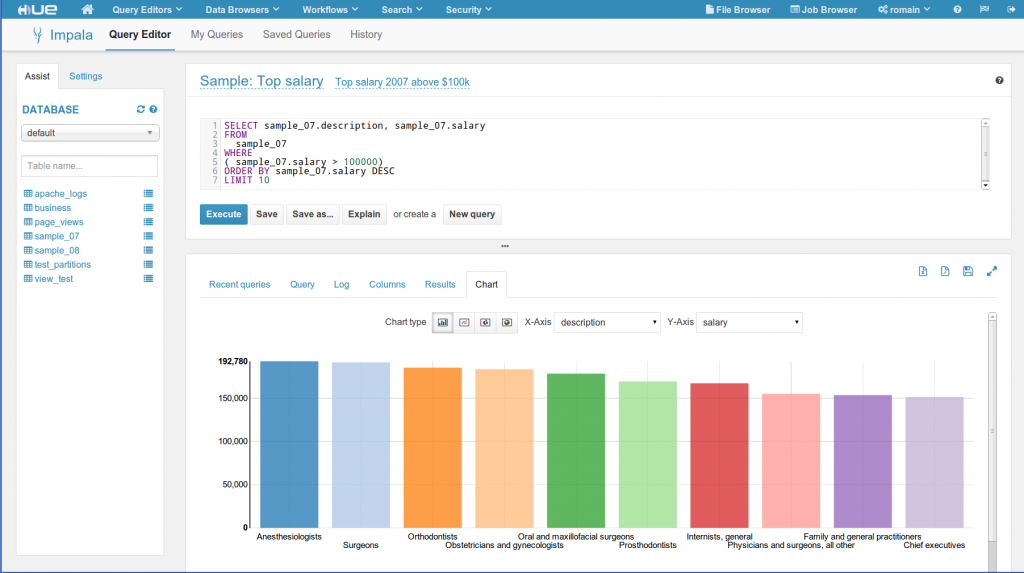
All queries were working and Hue is querying Hive/Impala and returning results!
As usual feel free to comment and send feedback on the hue-user list or @gethue!